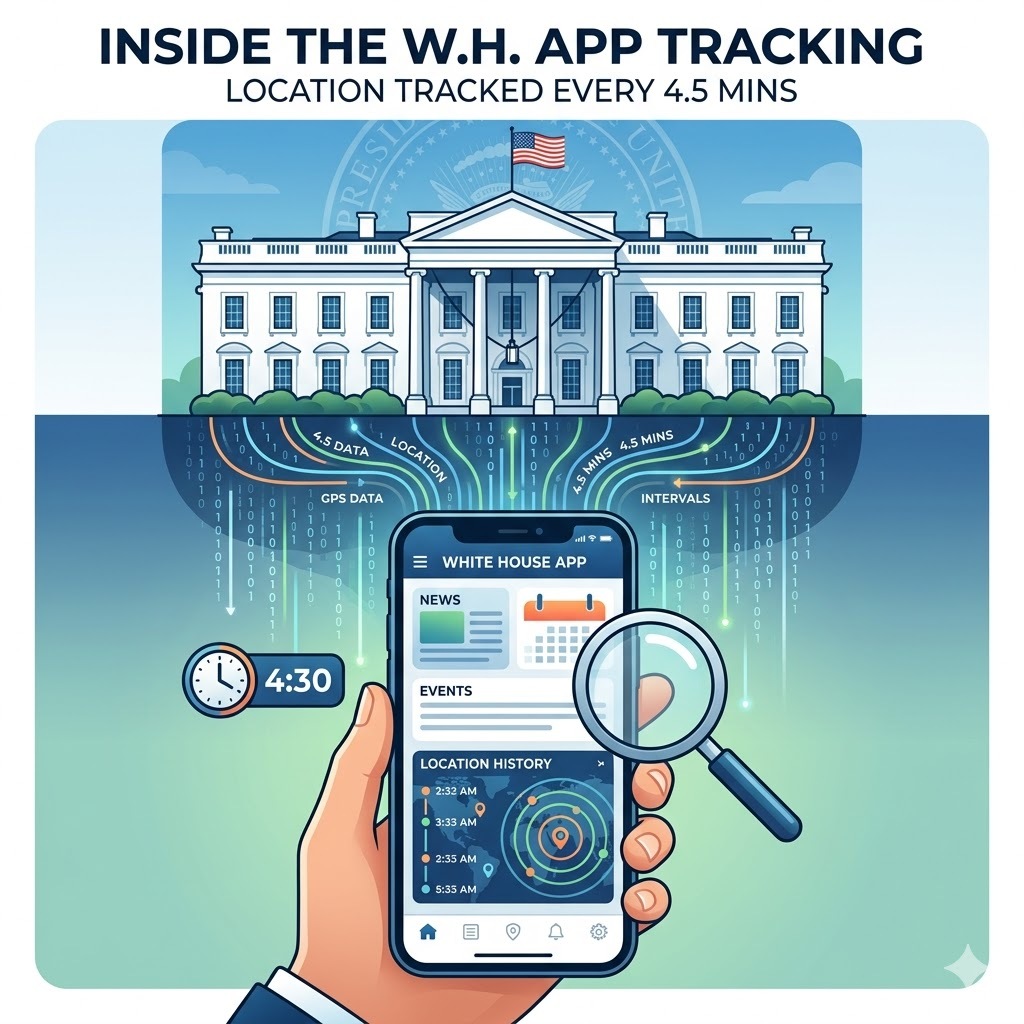
The official White House mobile app was launched on March 27, 2026, on Android and iOS. The app contains an embedded GPS pipeline capable of collecting user location coordinates every 4.5 minutes in the foreground and every 9.5 minutes in the background. It is a tracking interval built directly into the app’s compiled code, according to independent developer analysis of the app’s decompiled Android Package Kit published March 28, 2026.
The app was built by Dev Forty Five LLC, founded 9 days before the app’s release date. The Trump administration describes the app as delivering “unparalleled access” to the executive branch. Security researchers describe it as one of the most privacy-compromised government apps they have audited.
What the White House App Is and What It Claims to Do
White House app functionality presents itself as a direct communication channel between the Trump administration and the American public. The White House App bypasses traditional media outlets entirely.
The app’s 6 stated features are:
- Live streams of press briefings and events
- A media library of photos and videos
- Breaking news alerts and push notifications
- Policy initiative portals
- Social media feed consolidation
- A “Text President Trump” direct contact button
The app launched with a promotional post from the official White House X account on March 27, 2026, stating: “Live streams. Real-time updates. Straight from the source, no filter.” An ICE tip line is also embedded inside the app, providing a direct link to Immigration and Customs Enforcement’s tip submission form.
The Center for Democracy and Technology, a nonprofit advocating for transparency in government technology, responded to the launch with a direct statement: “Mobile apps can be a helpful tool for making government more accessible. But this administration has given people a lot of reasons to worry about their privacy, and this app only raises more questions about what the federal government is doing with our personal data.”
What Security Researchers Actually Found Inside the App
White House app security analysis began March 28, 2026, 1 day after launch, when independent developer @Thereallo1026 decompiled the app’s Android Package Kit and published findings on their blog. A second independent researcher, Atomic Computer Services, published parallel findings on the iOS version on the same day.
The 2 independent analyses conducted by @Thereallo1026 on Android and Atomic Computer Services on iOS identified overlapping concerns across the following 5 distinct security and privacy categories:
- GPS location tracking: foreground and background polling intervals hardcoded into the compiled build
- OneSignal SDK integration: a commercial third-party tracker serving location, analytics, and notification functions simultaneously
- iOS App Store privacy disclosure mismatch: the listing states no location data is collected, while the code contains an active GPS pipeline
- Third-party YouTube embed dependency: video code loading from a personal GitHub account rather than an official repository
- Removal of privacy consent banners: third-party content inside the app loads without displaying consent notifications to users
Let’s take a detailed look at these 5 distinct security and privacy categories.
GPS Location Tracking
GPS pipeline analysis of the decompiled Android APK found foreground location polling hardcoded to 270,000 milliseconds, exactly 4.5 minutes, and background polling hardcoded to 570,000 milliseconds, exactly 9.5 minutes.
The pipeline includes fused location requests, capture logic, background scheduling, and API sync to a third-party server. The withNoLocation Expo plugin, a tool specifically designed to strip location permissions from a React Native build before release, was present in the codebase but produced no effect. The full GPS pipeline compiled through regardless.
OneSignal SDK Integration
OneSignal, a U.S.-based technology company whose SDK serves location tracking, push notification, and analytics functions simultaneously, is the primary embedded tracker identified in the Android app. OneSignal’s full GPS pipeline, not just its notification module, was compiled into the app’s production build. The developer noted that user location data, notification interactions, and device identifiers are transmitted to OneSignal’s external servers during normal app use.
iOS App Store Privacy Disclosure Mismatch
Atomic Computer Services found that the iOS version of the White House app reported to the App Store that it did not collect location data. A disclosure that directly contradicts the GPS capability compiled into the app’s code. Whether active GPS collection occurs on iOS is unconfirmed, but the capability exists in the codebase regardless of the App Store disclosure. Atomic Computer’s published assessment stated: “We’ve audited apps for startups with three employees that had better security than this.”
Third-Party YouTube Embed Code
YouTube embed functionality inside the app pulls code from a personal GitHub account rather than from an official Google or government-controlled repository. A compromise of that personal GitHub account would affect every user of the White House app simultaneously, an attack surface that standard government application security protocols prohibit.
Removal of Privacy Consent Banners
Third-party content viewed inside the app loads without the privacy consent banners that those content providers normally display. Users viewing embedded external content receive no consent notification, disclosure, or opt-out mechanism.
| Security Issue | Platform | Severity Indicator |
| GPS foreground polling | Android | Every 4.5 minutes (hardcoded) |
| GPS background polling | Android | Every 9.5 minutes (hardcoded) |
| OneSignal SDK | Android | Location + analytics + notifications |
| App Store privacy disclosure | iOS | States no location collection |
| YouTube embed source | Android + iOS | Personal GitHub account |
| Privacy consent banners | Android + iOS | Removed from third-party content |
| Developer company age | Both | Founded 9 days before launch |
Who Built the White House App
White House app development was completed by Dev Forty Five LLC, a company registered on March 18, 2026, in Utah, exactly 9 days before the app’s March 27, 2026, launch, with Ty Nielson listed as its registered agent according to the Utah Division of Corporations and Commercial Code Business Registration. No public information about Dev Forty Five LLC’s broader operations, prior government contracts, or federal security compliance history existed at the time of publication.
No established government technology contractor with federal security clearance and compliance history was named as the developer. Standard federal application development for executive branch products follows security frameworks, including NIST SP 800-53 controls, FedRAMP compliance requirements, and OMB Circular A-130 data management standards, frameworks that prohibit undisclosed third-party location data collection in government-facing consumer applications.
The White House did not respond to press requests for comment on the developer identity or the security findings published on March 28.
What the App Contradicts in Federal Privacy Standards
Federal privacy standards for executive branch mobile applications have historically prohibited geolocation data collection without meeting 3 simultaneous requirements:
- Explicit user consent before collection begins
- Mandatory public disclosure of what data is collected and where it is transmitted
- Documented operational justification explaining why location data is necessary for the app’s stated function
The White House app’s GPS pipeline contradicts all 3 requirements. It collects location without disclosed consent, its iOS App Store listing actively states no location data is collected, and no operational justification exists for background GPS polling in an app whose stated purpose is delivering press briefings and policy updates. These 3 contradictions exist across both the Android and iOS platforms simultaneously.
The inclusion of OneSignal, a commercial third-party tracker, inside a government application creates a data pipeline from American users’ devices to a private company’s servers, routed through an app bearing the official branding of the executive branch.
Government-sponsored mobile apps serving informational functions are standard practice across federal agencies, including FEMA, the CDC, and the Department of Veterans Affairs. All 3 agencies follow the same 3 baseline standards in their consumer-facing applications:
- Explicit data collection disclosures that name every third-party SDK present in the build
- Third-party SDK limitation to tools with documented federal compliance histories only
- Background location polling prohibition in applications with no location-dependent functionality
The White House app meets none of these 3 baseline standards as currently configured.
Now, here’s a critical question!
Should You Download the White House App?
White House app download decisions require weighing 4 documented risks against the app’s informational value.
- First, background GPS polling transmits location coordinates every 9.5 minutes to OneSignal’s external servers without disclosed user consent.
- Second, the personal GitHub dependency creates a supply chain attack surface affecting all users simultaneously.
- Third, the iOS privacy disclosure actively misrepresents the app’s location capability to Apple’s App Store review system.
- Fourth, the developer’s 9-day company history provides no established security track record, compliance history, or accountability framework.
All content available inside the White House app, including live streams, press briefings, policy updates, and social media feeds, is accessible directly through the White House’s official website and verified social media accounts, without installing software that transmits location data to third-party servers every 4.5 minutes.
Download the White House app if the convenience of push notifications and consolidated access outweighs the 4 documented privacy risks for your specific use case. Delete it immediately if background location transmission to a third-party commercial server is unacceptable under your personal or professional privacy standards.
Conclusion
White House app security analysis confirms a government-branded application shipping with a live GPS pipeline, an undisclosed third-party location tracker, a mismatched App Store privacy disclosure, a personal GitHub dependency, and privacy consent banner removal, built by a company that did not exist 2 weeks before the app’s launch. The administration’s “no filter” positioning describes the content delivery accurately. It also describes the data collection pipeline with equal precision.
Technology, artificial intelligence, digital culture, and everything shaping the connected world, we cover it all. Subscribe to our newsletter and get the stories that matter, before everyone else does.