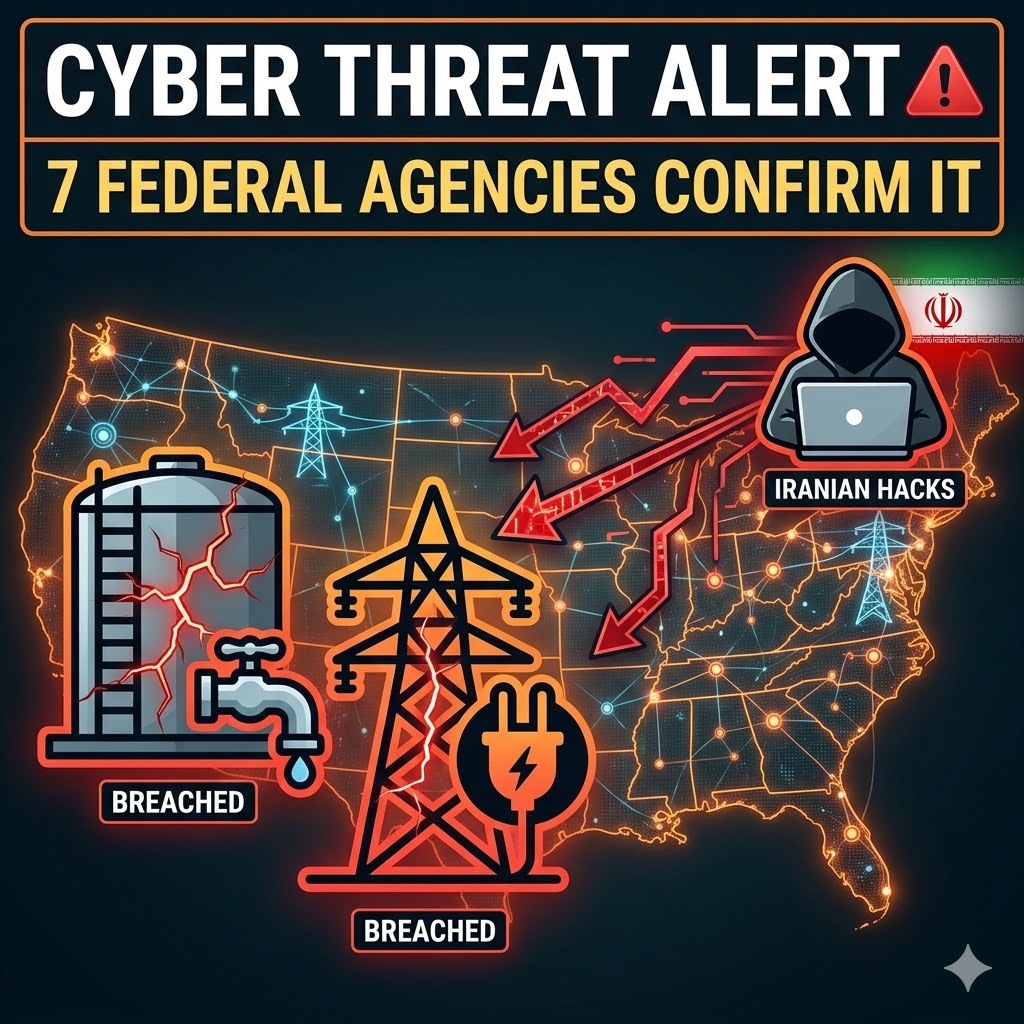
Iranian-affiliated hackers are actively exploiting vulnerabilities in US critical infrastructure control systems, according to a joint advisory published on April 7, 2026, by 7 federal agencies simultaneously: the Cybersecurity and Infrastructure Security Agency, the National Security Agency, the Federal Bureau of Investigation, US Cyber Command, the Department of Energy, the Environmental Protection Agency, and the Cyber National Mission Force.
The advisory confirms that attacks have already produced operational disruption and financial losses at unnamed US organizations across 3 sectors: energy, water and wastewater systems, and government services and facilities.
This is not a warning about a theoretical future threat. The damage has already occurred.
What the Hackers Are Targeting and How
Iran-linked advanced persistent threat actors are targeting programmable logic controllers, industrial computers that control physical equipment inside critical infrastructure networks. PLCs govern the mechanical operations of water treatment plants, power grid components, and government facility systems. They translate digital commands into physical actions: opening valves, adjusting pressure, controlling electrical loads, and managing chemical dosing in water treatment.
The specific devices being actively exploited are Rockwell Automation/Allen-Bradley PLCs, one of the most widely deployed industrial control system brands in North American infrastructure. CISA added a major Rockwell Automation vulnerability to its Known Exploited Vulnerabilities catalog in early March 2026, approximately 5 weeks before this advisory. Attackers are also targeting supervisory control and data acquisition displays, the operator interfaces that show engineers the real-time status of the physical systems PLCs are controlling.
The attack method exploits a single structural vulnerability: these devices are directly connected to the public internet. Industrial control systems were historically designed as isolated networks. As infrastructure operators moved toward networked efficiency, many PLCs gained internet connectivity without the security architecture that internet-facing systems require. Attackers found them, accessed them, and in several documented cases altered the data operators were seeing, manipulating display readings while extracting device project files containing system configuration data.
Ed Moreland, vice president of government affairs at Rockwell Automation, confirmed the company “takes seriously the security of its products and solutions seriously and has been closely coordinating with government agencies” on the advisory.
The Group Behind the Attacks
The advisory does not name the specific Iranian hacking group responsible but confirms the activity bears direct resemblance to operations conducted by CyberAv3ngers in 2023. CyberAv3ngers is affiliated with Iran’s Islamic Revolutionary Guard Corps, the IRGC, Iran’s primary military and intelligence force responsible for external operations.
CyberAv3ngers’ 2023 campaign targeted Israeli-made Unitronics digital control panels at multiple US water treatment facilities in Pennsylvania, defacing control interfaces and disrupting operations at sites including the Municipal Water Authority of Aliquippa. Those attacks occurred in direct response to the October 7, 2023, Hamas attack on Israel and subsequent Israeli military operations in Gaza, establishing the pattern that the 2026 advisory explicitly references.
The 2026 advisory states the escalation is “likely in response to hostilities,” specifically the ongoing US-Israel military operations against Iran that began in late February 2026. The advisory connects a documented geopolitical escalation to a documented cyber escalation with precision that the federal government rarely provides publicly.
Iran’s cyber escalation is not operating in isolation. Russian satellites conducted at least 24 documented reconnaissance surveys across 11 Middle Eastern countries during the same period, sharing targeting intelligence with Iran that directly preceded Iranian ballistic missile and drone strikes on US military assets in the region.
What 7 Federal Agencies Are Telling Infrastructure Operators Right Now
The joint advisory delivers 3 immediate operational directives to all US critical infrastructure organizations.
1. Remove PLC systems from direct internet exposure immediately. Any programmable logic controller or SCADA display accessible directly from the public internet represents an unacceptable attack surface under current threat conditions. Air-gapping or firewall-isolating these systems is the primary mitigation.
2. Audit logs for suspicious traffic now. Organizations should review available network and device logs for indicators of unauthorized access, unusual data transfers, or anomalous command sequences. The advisory’s confirmation that attackers altered display data in some cases means organizations cannot rely solely on what their monitoring screens are showing; the screens themselves may have been manipulated.
Federal cybersecurity guidance is reaching beyond infrastructure operators to individual device users simultaneously. The FBI has issued specific warnings to iPhone and Android users about the interception vulnerabilities and account takeover techniques that state-sponsored actors use to establish the initial access positions from which larger infrastructure campaigns are coordinated.
3. Contact Rockwell Automation directly if potentially targeted. Organizations running Rockwell Automation/Allen-Bradley equipment who suspect they may have been in the attack window should initiate direct contact with the manufacturer for device-level forensic assessment.
Kimberly Mielcarek, vice president of the North American Electric Reliability Corporation’s Electricity Information Sharing and Analysis Center, confirmed the organization sent an “all-points bulletin” to energy sector members following the advisory. “Our Watch Operations team is actively monitoring the grid, while we continue to coordinate closely with the Department of Energy, the Electricity Subsector Coordinating Council, and our federal and provincial partners,” she stated.
The Department of Energy confirmed involvement in active incident response: “Protecting America’s critical energy infrastructure is a top priority for the US Department of Energy,” a spokesperson told Politico, noting the department worked directly with other agencies on mitigation recommendations.
Why Critical Infrastructure Remains Vulnerable
The structural vulnerability this advisory exposes is not new and has not been resolved by previous warnings. Industrial control systems governing water treatment, power generation, and government facilities were designed decades before internet connectivity was standard, built for reliability and physical access, not networked security. As operational efficiency pressures pushed infrastructure operators to connect these systems to corporate networks and the internet, the security architecture did not follow.
The result is a documented, recurring pattern: state-sponsored threat actors identify internet-exposed industrial control systems through standard scanning tools, exploit default credentials or unpatched vulnerabilities, and gain access to the physical systems that deliver water and electricity to millions of people. The 2021 Oldsmar, Florida water treatment facility attack, where an attacker remotely increased sodium hydroxide levels to 111 times the normal concentration before an operator noticed, used the same attack surface this advisory addresses.
This recurring pattern is not isolated to Iranian actors or US targets. The two-decade global record of significant state-sponsored and criminal cyberattacks establishes that internet-exposed industrial control systems have been a documented priority target across every major threat actor category operating today.
| Attack | Year | Target | Actor | Method |
| Oldsmar Water Treatment | 2021 | Florida water facility | Unattributed | Remote access via internet-exposed HMI |
| CyberAv3ngers PA Water | 2023 | Pennsylvania water authorities | Iran/IRGC | Exploited Unitronics PLCs |
| 2026 Infrastructure Campaign | 2026 | US energy, water, and government | Iran/IRGC-affiliated | Internet-exposed Rockwell PLCs |
Final Takeaway
The warning is correct. The gap between warning and action is the problem.
Seven federal agencies issuing a joint advisory is the US government’s highest-credibility threat communication mechanism. The operational guidance is sound: remove PLCs from internet exposure, audit logs, and contact affected vendors. Acting CISA Director Nick Andersen stated as recently as March 2026 that the agency had “not seen a rise in threat actor activity” linked to Iran since the war began, a statement this April 7 advisory implicitly contradicts.
The contradictory position targets the structural pattern that this advisory repeats. US federal agencies have issued warnings about internet-exposed industrial control systems and Iranian targeting of critical infrastructure in 2021, 2022, 2023, and now 2026. Each advisory describes the same attack surface. Each advisory recommends the same primary mitigation: remove systems from internet exposure. The same vulnerabilities that enabled the 2023 Pennsylvania water treatment attacks enabled the 2026 campaign. A threat advisory that accurately describes an attack and correctly prescribes the mitigation, issued for the fourth consecutive cycle against the same attack surface, raises a question the advisory itself does not answer: why are these systems still internet-exposed?
State-sponsored cyberattacks, critical infrastructure security, and the federal advisories shaping how organizations defend against active threats are covered at The IT Horizon. Subscribe to our newsletter. We translate every CISA advisory, threat actor disclosure, and infrastructure vulnerability into what your organization actually needs to do.